In the ever-evolving digital landscape, safeguarding your assets and achieving your objectives demands cutting-edge expertise. Our group of expert hackers delivers tailored solutions that are both stealthy and powerful. We specialize in a wide range of services, including security audits, evidence extraction, and risk management. Our approach is centered around analyzing your unique needs and developing strategies that maximize your security posture. We are committed to providing trustworthy results with the strictest privacy protocols.
Demand a Hacker? We Supply Results - Guaranteed
Looking for discreet hackers to crack your goal? Look no further! Our team of top-tier ethical hackers is ready to manage any get more info difficult task you offer our way. We assure results, every time.
Our capabilities include network penetration testing, data retrieval, website defacement, and more.
We operate with the utmost measures of security to protect your anonymity. Contact us today for a free consultation. We're ready to explore your wants.
Unearth Hidden Data with Expert Ethical Hacking
In today's cyber landscape, data is king. Organizations strive to harness its potential for growth and advancement. However, latent data often persists untapped, posing a considerable challenge. Ethical hacking emerges as a vital tool to analyze these systems, exposing valuable intelligence that can transform your business. Our team of certified ethical hackers implements a range of advanced techniques to identify hidden data, providing you with actionable insights for a strategic advantage.
Hire a Pro Hacker: Security Audits & Penetration Testing
In today's digital landscape, safeguarding your network against cyber threats is paramount. A thorough approach to protection involves regularly evaluating your vulnerabilities. This is where engaging a professional hacker, also known as a penetration tester, comes into play.
Penetration testing simulates real-world cyberattacks to identify weaknesses in your firewalls. A skilled penetration tester will exploit these vulnerabilities to reveal potential breaches before malicious actors can utilize them.
- Benefits of hiring a Pro Hacker:
- Improved Security Posture
- Anticipatory Threat Detection and Mitigation
- Reduced Risk of Data Breaches
- Elevated Confidence in your systems
By conducting regular security audits and penetration testing, you can fortify your defenses against the ever-evolving threat landscape. Remember, a proactive approach to cybersecurity is essential for protecting your valuable data and assets.
Discreet Cyber Warfare: Your Reliable Hacker Team
In the ever-evolving landscape of digital warfare, maintaining a competitive edge necessitates expertise that goes beyond traditional strategies. Our elite team of hackers offers secure cyber warfare operations tailored to your individual needs. We perform a wide spectrum of missions, including reconnaissance, system infiltration, data acquisition, and countermeasures.
Our dedicated team operates with the utmost concealment, ensuring your operations remain untraceable. We employ the latest technologies and strategies to ensure optimal success. Whether you need to identify vulnerabilities, acquire critical data, or counter your opponents's systems, our team is here to provide the knowledge you need to achieve your objectives.
Digital Fortress Breach : Professional Hackers at Your Command
Within the digital domain, where information reigns supreme, there exists a select group of individuals known as professional hackers. These skilled operatives possess the abilities to penetrate even the most secure systems. Imagine having access over these digital experts, their prowess at your command.
Whether you require to test the integrity of your own defenses or need a specific action within the digital realm, professional hackers can be your unseen weapon. They operate in the shadows, their skills honed through years of practice.
- Unleash the power of penetration testing to identify vulnerabilities before they can be exploited.
- Secure confidential information with surgical precision, leaving no trace behind.
- Bypass firewalls and other security measures with ease.
But proceed with caution. The power of professional hackers is a double-edged sword. Leverage their skills responsibly, always within the bounds of law.
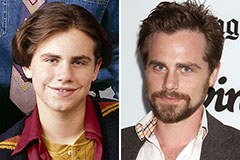 Rider Strong Then & Now!
Rider Strong Then & Now! Daniel Stern Then & Now!
Daniel Stern Then & Now! Kelly McGillis Then & Now!
Kelly McGillis Then & Now! Nancy McKeon Then & Now!
Nancy McKeon Then & Now! Peter Billingsley Then & Now!
Peter Billingsley Then & Now!